Always scroll to the bottom of the page for the main download link.
We don't believe in fake/misleading download buttons and tricks. The link is always in the same place.
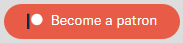
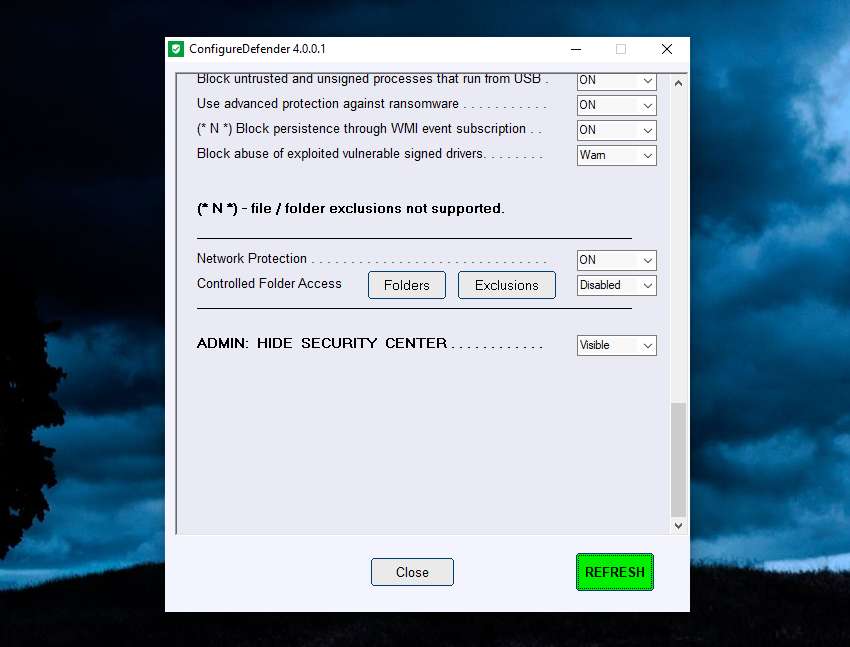
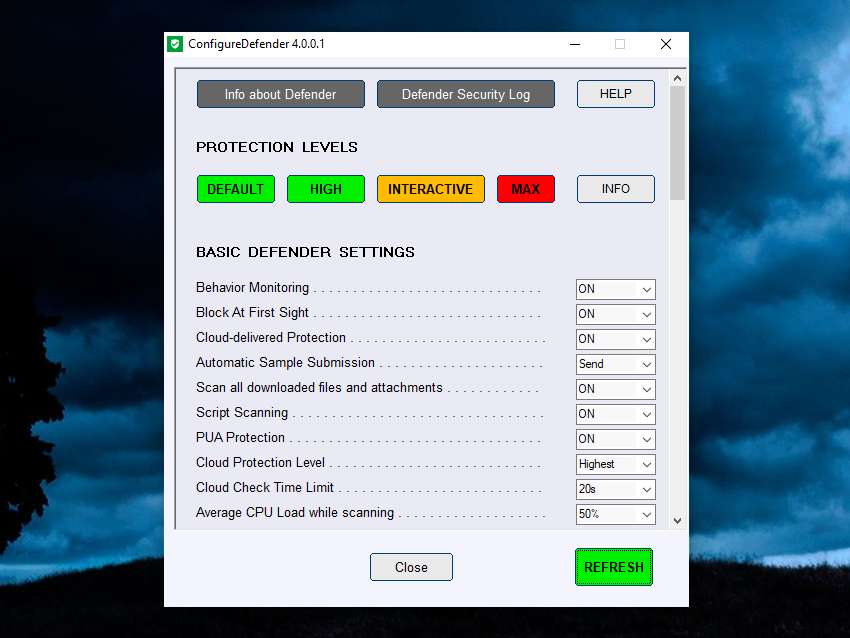
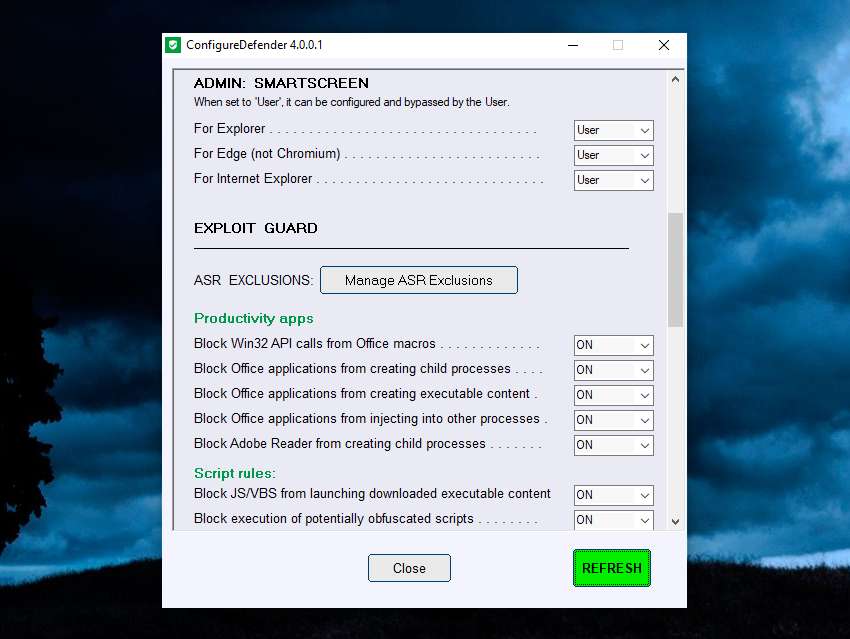
ConfigureDefender v4.0.0.1
A small utility for configuring Windows 10, 11 and Server's built-in Defender Anti-Virus settings.
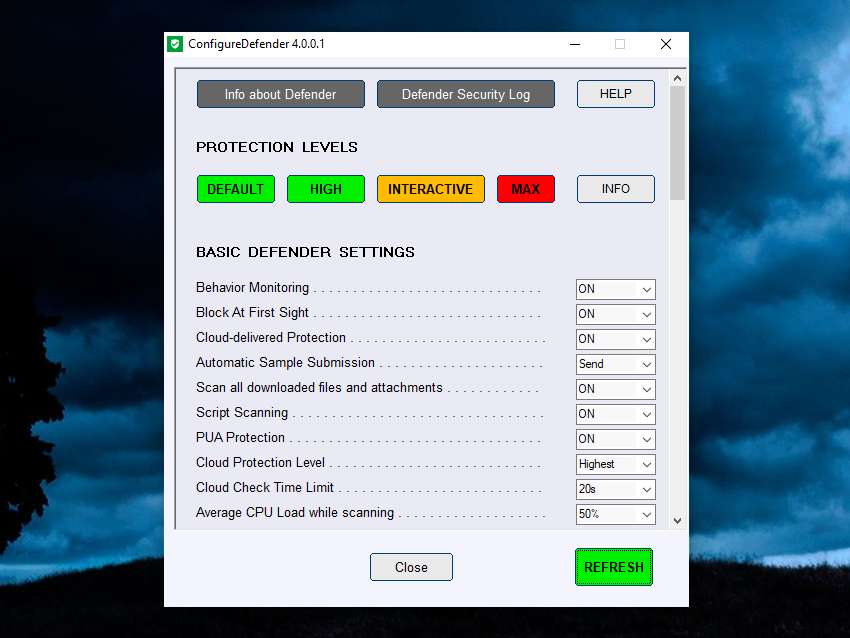
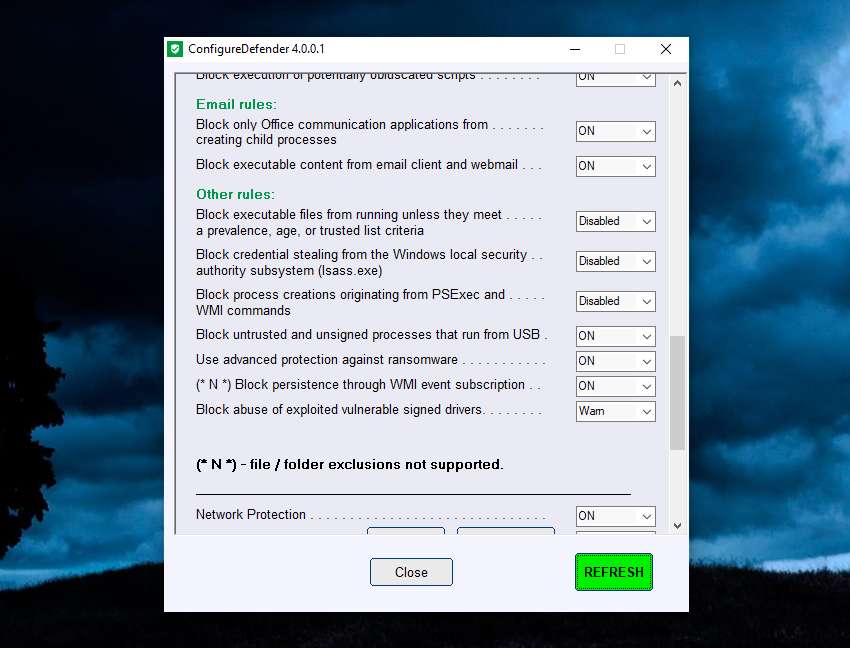
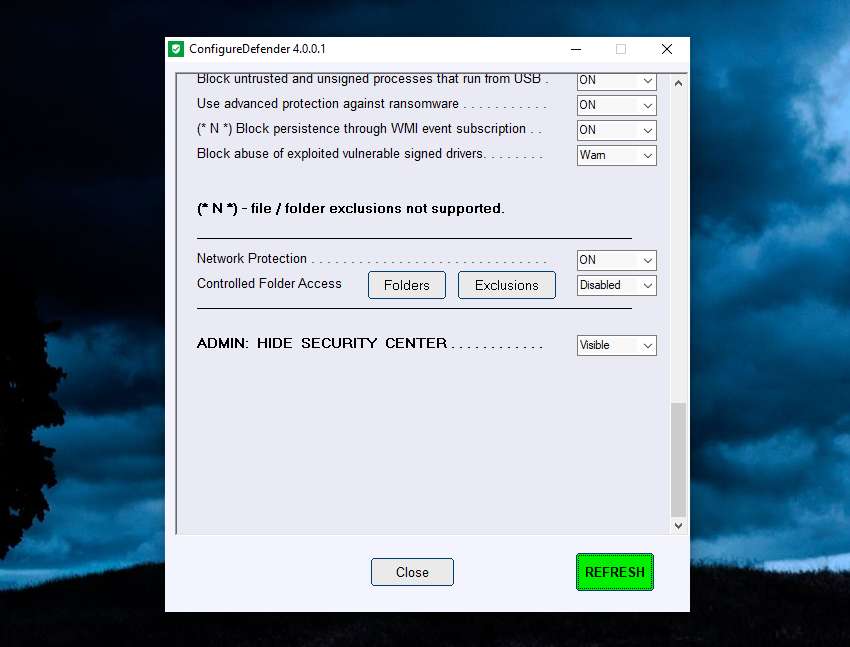
ConfigureDefender utility is a small GUI application to view and configure important Defender settings on Windows 10/11 and Windows Server 2019+. It uses PowerShell cmdlets (with a few exceptions) to change the Windows Defender settings. Furthermore, the user can apply one of three pre-defined protection levels: DEFAULT, HIGH, INTERACTIVE, and MAX. Changing one of the protection levels requires a reboot to take effect.
Using the Maximum Protection Level
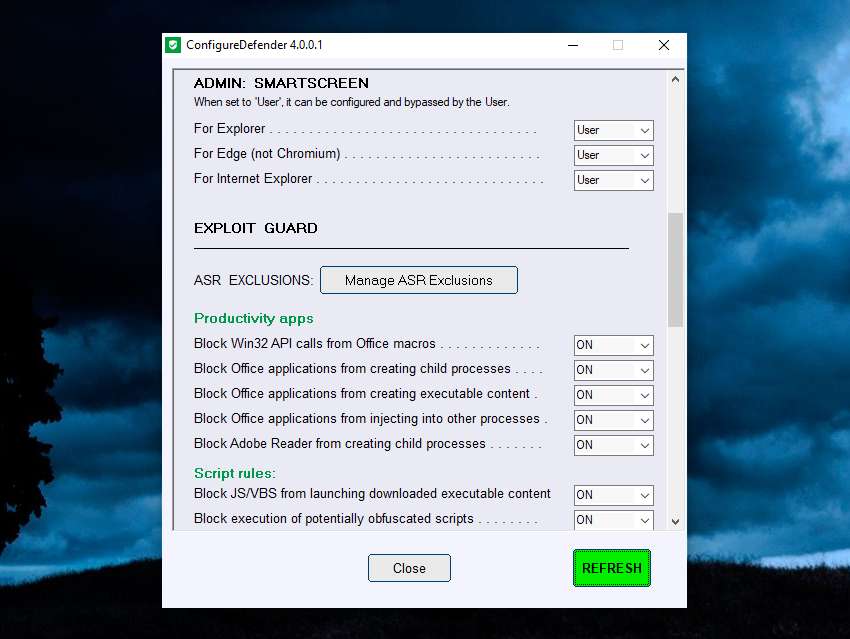
The MAX Protection Level blocks anything suspicious via Attack Surface Reduction, Controlled Folder Access, SmartScreen (set to block) and cloud level (set to block) - Defender Security Center is hidden. These settings are very restrictive and using them can produce many false positives even in the home environment. Such a setup is not recommended in the business environment.
Advanced Users
Some important remarks on the possible ways used to configure Defender (for advanced users).
Windows Defender settings are stored in the Windows Registry and most of them are not available form Windows Defender Security Center. They can be managed via:
• Group Policy Management Console (gpedit.msc is not available in Windows Home edition)
• Direct via Registry editing (manually, via *.reg files or scripts)
• PowerShell cmdlets (set-mppreference, add-mppreference, remove-mppreference, PowerShell 5.0).
Windows Defender Registry Keys
Normally, Windows Defender stores most settings under the key (owned by SYSTEM):
Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender
The registry keys can be changed while using Defender Security Center or PowerShell cmdlets.
Overwriting settings via Group Policy Management Console (GPO)
Administrators can use Windows Group Policy Management Console (GPO) utility to override certain Windows Defender registry values. Group Policy settings are stored under another key (owned by ADMINISTRATORS):
Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender
Keep in mind that GPOs do not delete the normal Defender settings!
Manually changing WD settings via registry
Registry editing is usually made, under the second key (see below), the first requires system admin-rights. Applying Defender settings by directly manipulating the registry under:
`Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender
is not recommended (!) on Windows 10 editions which officially supporting Group Policy Management Console e.g. PRO and Enterprise editions.
Those settings are not recognized by Group Policy Management Console.
They can temporarily overwrite Group Policy Management Console setup in the Registry, because they share the same Registry keys. Those changes are not permanent, because Group Policy configuration is not overwritten.
After some hours, those settings are automatically and silently back-overwritten by Group Policy Refresh feature.
Those settings cannot be changed via Defender Security Center (or PowerShell cmdlets), even if they are visible (like folders and applications related for Controlled Folder Access).
Windows 10/11 Home Editions
Under Windows 10/11 Home editions, someone can configure Defender settings (outside of the Defender Security Center), when using PowerShell cmdlets or via the manual Registry editing method. This may confuse some users, but ConfigureDefender utility can remove the settings made under the following path:
Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender
This is required, because those settings would override ConfigureDefender settings.
ConfigureDefender utility and GPOs
ConfigureDefender utility can be used on Windows 10 Professional & Enterprise editions, if an Administrator did not apply Defender policies via Group Policy Management Console. Normally, all those policies are by default set to 'Not configured'. They can be found in Group Policy Management Console:
Computer configuration >> Policies >> Administrative templates >> Windows components >> Windows Defender Antivirus.
The tabs: MAPS, MpEngine, Real-time Protection, Reporting, Scan, Spynet, and Windows Defender Exploit Guard, should be inspected before using ConfigureDefender. The corresponding policies have to be set to 'Not configured'. If not, then the GPO Refresh feature will override the settings applied via ConfigureDefender.
Available Windows Defender settings on different Windows 10/11 versions
• Configuredefender requires Windows ver. 1809 or later.
• The ASR rule "Block persistence through WMI event subscription" requires Windows ver. 1903 or later.
Download Manual
Click here to visit the author's website.
Continue below for the main download link.
|










 , out of 34 Votes.
, out of 34 Votes.